Initial and global assesment
Site visit and processing initial comments and shortcomings. Initial assessment. First evaluation, recommendations and solution proposal. Determination and offer for the requested support. Senior expert involved from beginning to the end of the project. For do it your self, our book is a good practice guideline.
Audit and data analytics

Site audit. Current system data analytics Control of existing system information. Presentation of contemporary technologies within scope of project.
New risk assessment

Bring stakeholders concerns and experts information on the table. Establish a new up to date risk analysis. Define guidelines to budget spending correspondent to risk factors. Creation of confidential security book.
First installation and budget approach

First elaborated schematic of project layout. Quantities Excel file and early budget update. Chapter 2 creation in confidential security book explaining choices made.
Solution debate and budget parts allocation

Presentation and all stakeholders debate on solution and budget. Discussion on impact on safety regulations.
Concretization

Finalization of project concept. Measurements and feasability study. Equipment implant area per area.
Specification

Creation of a book of specifications for the equipment to be used. Each equipment and software has to be conform the book of specifications.
Re-budgeting and ROI

Re-budgeting and evaluation of the return on investment.
Installation definition

Creation of the book of installation defining exact position of all equipment and referenced to the book of specifications.
Planning
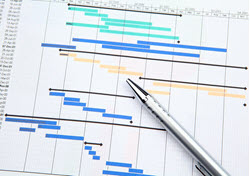
Planning and sequence of execution. Installation, training, test phase, commissioning have to be programmed in correct order.
Follow-up of execution and training

Control of physical and logical execution. Reporting. Training evaluation. Commissioning.
Annual test and database analytics

Periodic system verification.System data analysis and error or fraud detection.
Final documents established for different parties.
Installation
Specification
Confidential Security